Standing Up a Microsoft Certificate Authority - Part 4
This post is one in a series about setting up a Microsoft Certificate Authority. It's broken down into the following parts.
- Part 1 - Standing up your Root CA
- Part 2 - Standing up your Subordinate/Issuing CA
- Part 3 - Catch up on what we've done and how it works
- Part 4 - Trusting your Root CA across the domain (You Are Here)
- Part 5 - Setting up Certificate Templates
- Part 6 - Using Computer, Web Server, and Code Signing Certificates
- Part 7 - Using the Certificate Enrollment Web Interface
- Part 8 - Maintenance and your day to day work
- Part 9 - So you want to learn more?
This is an introduction to CAs only, and I’ll admit that all of my knowledge is from working with consultants to stand environments up and from reading Microsoft’s documentation. Make sure you do your own research to properly secure your CA and stand it up in a way that works best for your environment. A personal shout out again to my technical editor for this series, Anthony Fontanez.
In this post we’re going to setup the trust for your Root Certificate in your environment. If we think about what we talked about back in Part 1 of this series, you’ll remember that once we trust the guy at the top, we trust anyone down the chain as well. By trusting your Root Certificate, we automatically trust your intermediate certificate and anyone who your intermediate authority generates a certificate for.
In this lab, we’re going to create a brand new GPO for the purpose of trusting the certificate, but in yours you may decide it makes more sense to add the certificate to an existing policy. Doesn’t make a difference so long as the policy applies to the clients that will need to trust this certificate chain.
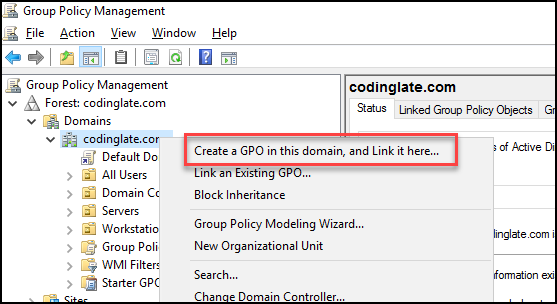
We’ll start by opening the Group Policy Management Console from any client on the network with access to it. We’re then going to right click on the domain or OU that we need the policy to apply to, and select “Create a GPO in this domain, and Link it here”. For my lab, I’m going to create this GPO right at the root of the domain, as pictured.
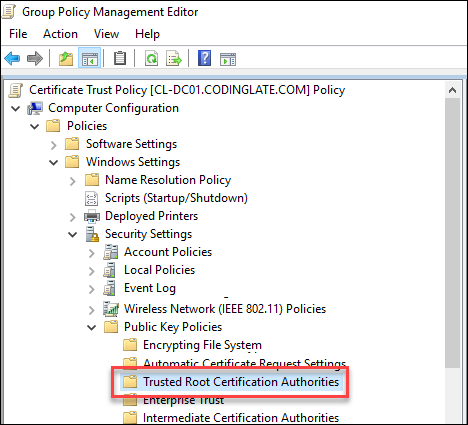
I’ll give mine the name “Certificate Trust Policy” and click OK. I’ll then right click on the GPO and select to Edit it. You’ll find the policy you want to modify under Computer Configuration -> Windows Settings -> Security Settings -> Public Key Policies -> Trusted Root Certification Authorities, as shown in the image.
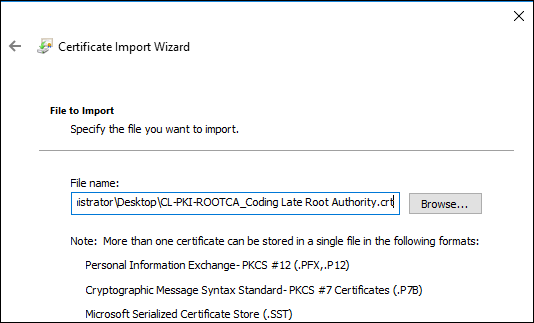
Right click on this folder and select the option to Import. On the first screen of the wizard there will be no selectable option, so click Next, and then browse out to the Root CA certificate file. This will be stored in the C:\Windows\System32\CertSrv\CertEnroll folder on your intermediate server. You’re importing the certificate into the GPO and not simply referencing a folder location, so it’s OK if you need to copy this file around to import it. Make sure you’re not accidentally copying the CRT file for your subordinate CA!
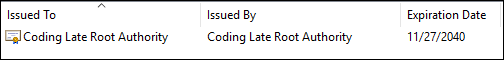
Accept the defaults for the rest of the import and the certificate should appear in the list. The Issued To and Issued By should be the same, otherwise you’ve mistakenly imported the Intermediate Certificate instead of the Root CA. No harm, you can delete it and import the right one if you’ve made a mistake.
Congratulations, you now have a Root Certificate Authority, an Issuing or Intermediate Certificate Authority, and you have them trusted throughout your domain. Perhaps time to start getting ready to issue some certificates?
Next: Part 5 - Setting up Certificate Templates
No comments