Standing Up a Microsoft Certificate Authority - Part 7
This post is one in a series about setting up a Microsoft Certificate Authority. It's broken down into the following parts.
- Part 1 - Standing up your Root CA
- Part 2 - Standing up your Subordinate/Issuing CA
- Part 3 - Catch up on what we've done and how it works
- Part 4 - Trusting your Root CA across the domain
- Part 5 - Setting up Certificate Templates
- Part 6 - Using Computer, Web Server, and Code Signing Certificates
- Part 7 - Using the Certificate Enrollment Web Interface (You Are Here)
- Part 8 - Maintenance and your day to day work
- Part 9 - So you want to learn more?
This is an introduction to CAs only, and I’ll admit that all of my knowledge is from working with consultants to stand environments up and from reading Microsoft’s documentation. Make sure you do your own research to properly secure your CA and stand it up in a way that works best for your environment. A personal shout out again to my technical editor for this series, Anthony Fontanez.
In this post, we'll discuss how to use the Certificate Enrollment Web Interface that we installed back in Part 2 of this series. The web interface doesn't seem to be widely used since the Certificates MMC snap-in does most of the work, but it's useful to know it's there.
Configuring HTTPS
While the web server can be accessed over HTTP for viewing pending requests one has, downloading the Certificate Authorities Certificate Chain (what you deployed in Part 4 of this series), and even submitting encoded certificate request files, to submit a new request from the browser for a certificate, the server must accept requests over HTTPS.
Since we already covered how to set this up in part 6 of this series, we don't need to step through it again. If you need to allow for brand new requests generated through the browser, you'll want to ensure you set this up before you go live.
Accessing the Website
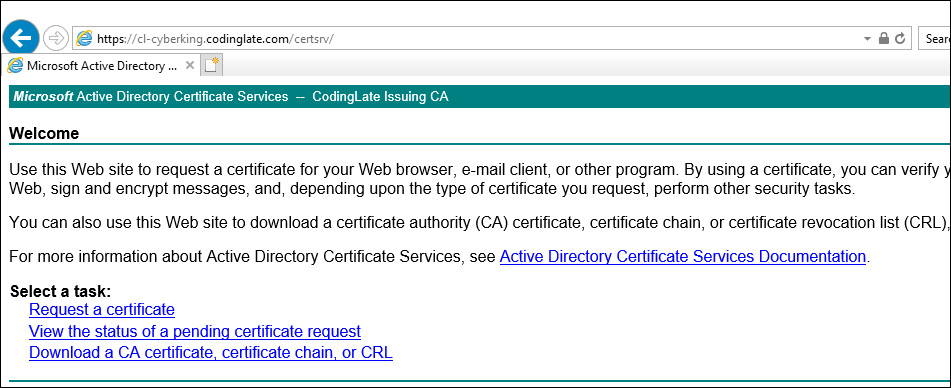
By default, you'll find the web interface at /certsrv on the webserver you've setup. Recall in part 2 of this series that we installed this feature on the CyberKing VM, so we'll access the interface at http://cl-cyberking.codinglate.com/certsrv/.
If everything works OK, you should see a screen similar to the one displayed below.
Requesting a Certificate
In order to request a certificate, you must be using Internet Explorer. Modern browsers will not allow for certificate requests. Once you've connected to the page, select the Request a Certificate link.
Next, you'll need to define the type of certificate you're going to request:
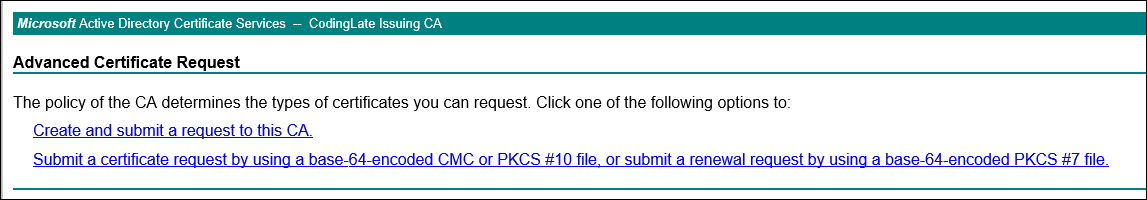
Create and submit a request to this CA
This is similar to the requests you made in part 6 of this series to request new certificate types. Along with the page loading using HTTPS, covered above, it must also be in either your Trusted Sites List or in your Local Intranet Zone. In most cases, your entire domain is probably already in your Local Intranet zone within Internet Explorer, but the page won't fully load if it is not.
Once you click on this option, your first choice will be to select a certificate template. You'll recognize these as the templates you made available in Part 5 of this blog series.
The options requested will vary based on the template you select. Once you complete the form and submit it, the key will be generated and you can download it. You should save it immediately. This key can then be imported into your Windows certificate store, or used for whatever purpose you were planning to use this certificate for.
Submit a certificate request by using a base-64-encoded CMC or PKCS #10 file, or submit a renewal request by using a base-64-encoded PKCS #7 file
This will be a request file that gets generated by another application or appliance in your environment. These are often known as CSRs, or Certificate Signing Requests. If you've ever ordered a certificate for your website, you may be familiar with these.
The following is an example CSR you can use if you'd like to test this from the DigiCert Sample Page:
1-----BEGIN CERTIFICATE REQUEST-----
2MIICvDCCAaQCAQAwdzELMAkGA1UEBhMCVVMxDTALBgNVBAgMBFV0YWgxDzANBgNV
3BAcMBkxpbmRvbjEWMBQGA1UECgwNRGlnaUNlcnQgSW5jLjERMA8GA1UECwwIRGln
4aUNlcnQxHTAbBgNVBAMMFGV4YW1wbGUuZGlnaWNlcnQuY29tMIIBIjANBgkqhkiG
59w0BAQEFAAOCAQ8AMIIBCgKCAQEA8+To7d+2kPWeBv/orU3LVbJwDrSQbeKamCmo
6wp5bqDxIwV20zqRb7APUOKYoVEFFOEQs6T6gImnIolhbiH6m4zgZ/CPvWBOkZc+c
71Po2EmvBz+AD5sBdT5kzGQA6NbWyZGldxRthNLOs1efOhdnWFuhI162qmcflgpiI
8WDuwq4C9f+YkeJhNn9dF5+owm8cOQmDrV8NNdiTqin8q3qYAHHJRW28glJUCZkTZ
9wIaSR6crBQ8TbYNE0dc+Caa3DOIkz1EOsHWzTx+n0zKfqcbgXi4DJx+C1bjptYPR
10BPZL8DAeWuA8ebudVT44yEp82G96/Ggcf7F33xMxe0yc+Xa6owIDAQABoAAwDQYJ
11KoZIhvcNAQEFBQADggEBAB0kcrFccSmFDmxox0Ne01UIqSsDqHgL+XmHTXJwre6D
12hJSZwbvEtOK0G3+dr4Fs11WuUNt5qcLsx5a8uk4G6AKHMzuhLsJ7XZjgmQXGECpY
13Q4mC3yT3ZoCGpIXbw+iP3lmEEXgaQL0Tx5LFl/okKbKYwIqNiyKWOMj7ZR/wxWg/
14ZDGRs55xuoeLDJ/ZRFf9bI+IaCUd1YrfYcHIl3G87Av+r49YVwqRDT0VDV7uLgqn
1529XI1PpVUNCPQGn9p/eX6Qo7vpDaPybRtA2R7XLKjQaF9oXWeCUqy1hvJac9QFO2
1697Ob1alpHPoZ7mWiEuJwjBPii6a9M9G30nUo39lBi1w=
17-----END CERTIFICATE REQUEST-----
If you request a certificate using this CSR, your Certificate Authority will issue a certificate to example.digicert.com.
You can also generate these requests using CERTUTIL, but as each case is unique on what you'd be requesting, and it'd likely be part of the documentation for whatever was needed in your environment, we'll keep it out of the scope of this post.
Next: Part 8 - Maintenance and your day to day work
No comments