Standing Up a Microsoft Certificate Authority - Part 8
This post is one in a series about setting up a Microsoft Certificate Authority. It's broken down into the following parts.
- Part 1 - Standing up your Root CA
- Part 2 - Standing up your Subordinate/Issuing CA
- Part 3 - Catch up on what we've done and how it works
- Part 4 - Trusting your Root CA across the domain
- Part 5 - Setting up Certificate Templates
- Part 6 - Using Computer, Web Server, and Code Signing Certificates
- Part 7 - Using the Certificate Enrollment Web Interface
- Part 8 - Maintenance and your day to day work (You are Here)
- Part 9 - So you want to learn more?
This is an introduction to CAs only, and I’ll admit that all of my knowledge is from working with consultants to stand environments up and from reading Microsoft’s documentation. Make sure you do your own research to properly secure your CA and stand it up in a way that works best for your environment. A personal shout out again to my technical editor for this series, Anthony Fontanez.
In this post we're going to talk about the operational work associated with managing the Microsoft CA. There are three things we'll touch on here. First, manually updating your Root CA CRL which should be done based on how you setup your CA. In this lab, that would be at least once every 6 months. Second, we'll talk about how to approve pending certificate requests. Finally, we'll cover how to revoke certificates that either no longer required, or that may have become compromised.
Updating the Root CA CRL
To generate an updated CRL, return to your offline Root CA. Open an elevated command prompt and execute the following command:
1certutil -crl
You should see a message that the command completed successfully. By default, you can get the updated CRL from C:\Windows\System32\CertSrv\CertEnroll (we set this up in part 1). You'll need to copy this CRL into the paths you setup in part 2 of this series, which in this lab was C:\WINDOWS\SYSTEM32\CERTSRV\CERTENROLL on your issuing CA.
Approve Pending Certificate Requests
Certificate requests can either be automatically approved based on the permission of the requester, or can be configured within the template to require the approval of a Certificate Authority Administrator. If you need a refresher on how certificate template work, return back to Part 5 of this series.
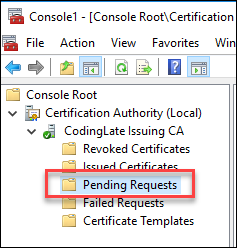
Certificate requests pending approval will appear in the "Pending Requests" folder of the Certificate Authority Snap-in. You can approve or reject requests by right clicking on the individual request(s) and using the pop-up context menu.
Revoking Certificates
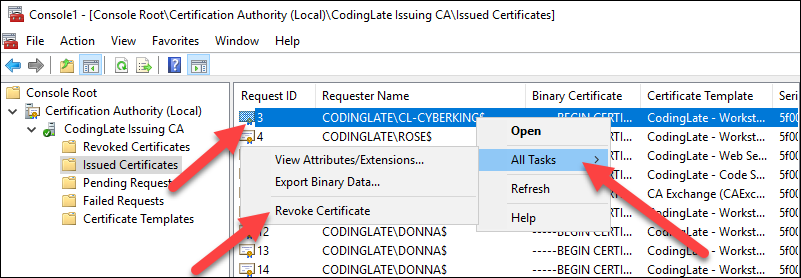
Certificates can be revoked before they expire naturally in the same Certificate Templates snap-in described in the above section. Simply right click on the certificate, followed by All Tasks and then Revoke Certificate. Note that certificates may be considered valid until the next time the the CRL (Certificate Revocation List) is checked the system verifying the authenticity of a specific certificate.
No comments